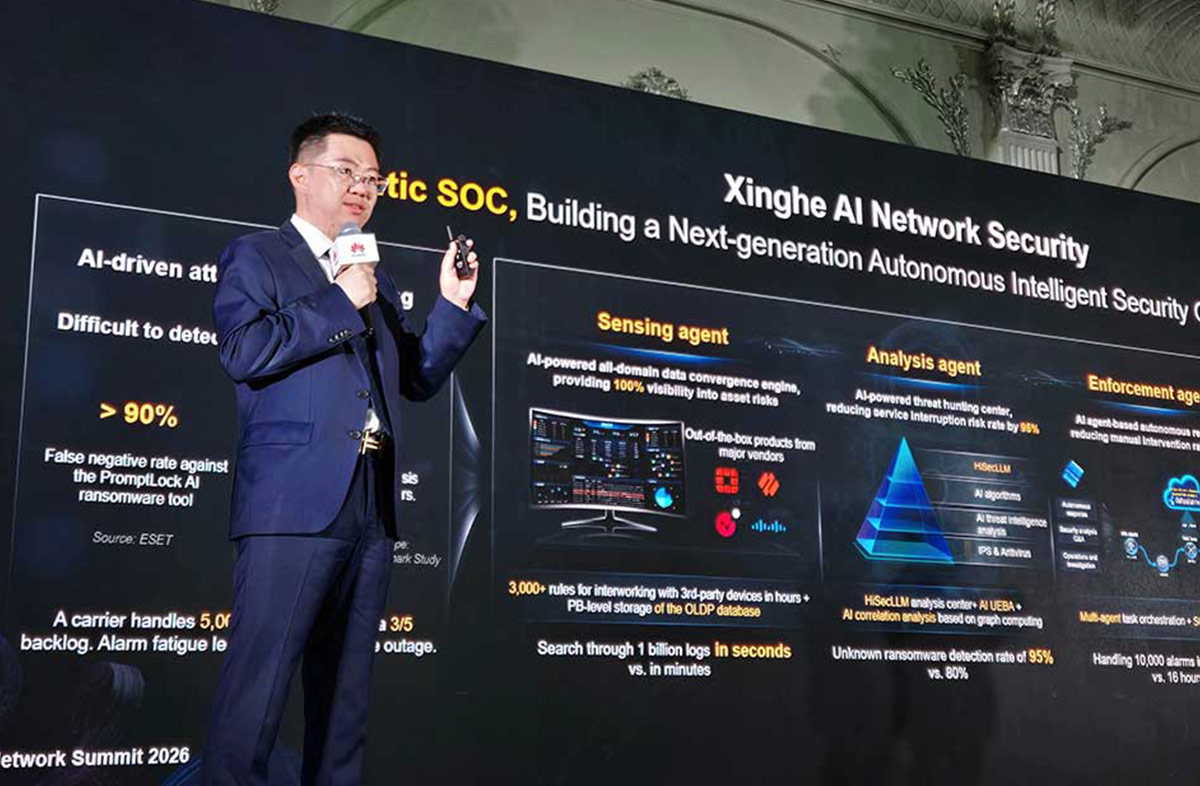
Huawei introduced its new Xinghe AI Network Security Agentic SOC (Security Operations Center) solution during the Huawei Network Summit 2026 Nor...

Bulgaria Adopts Amendments to the Cybersecurity Act in Line with NIS 2
The National Assembly adopted, at second reading, amendments to the Cybersecurity Act introducing expanded European requirements for risk assessment and incident reporting. With these changes, Bulgaria transposes the provisions of the NIS 2 Directive, aimed at achieving a high level of security of network and information systems across the European Union.
Expanded scope of the law
The new legislation significantly broadens the scope of affected organizations. In addition to previously covered entities, it now includes:
- public and private organizations
- providers of qualified trust services
- domain name registries
- educational institutions conducting critical scientific research
- judicial authorities
The number of sectors covered by the law increases from 8 to 18, with new additions including:
- space sector
- wastewater management
- ICT services between enterprises
- postal and courier services
- waste management
- production and distribution of chemicals and food
- manufacturing industries (including medical devices, electronics, machinery, and automotive)
- providers of digital services
- scientific research
New incident reporting requirements
The law introduces stricter rules for notifying cyber incidents. Organizations classified as essential and important must:
- notify the relevant sectoral CSIRT team within 24 hours of detecting an incident
- within 72 hours provide updated information and an initial assessment (including severity, impact, and technical details)
- submit a final report within one month after the update
For providers of trust services, the deadline for updating information is 24 hours.
Control over technologies used
The adopted amendments also introduce mechanisms for controlling the technologies used. Upon proposal by the Cybersecurity Council, the Council of Ministers may require organizations to use:
- specific ICT products and services
- technologies certified under European cybersecurity schemes
- solutions proven effective from both operational and economic perspectives
Additionally, at the EU level, risk assessments may lead to proposals to restrict certain technologies or supply chains, particularly when originating from non-EU countries.
If a technology is restricted by a government decision, organizations must discontinue its use within three years, except in cases of high national security risk, where the deadline may be shorter.
Importance of the changes
According to the acting Minister of e-Government, the adoption of these amendments marks an important step toward strengthening Bulgaria’s national cybersecurity.
The new rules aim to improve risk management, incident response, and control over critical technologies, while aligning national legislation with European standards.
Microsoft introduced a new PostgreSQL extension for Visual Studio Code that allows developers to manage PostgreSQL databases directly from the e...
Red Hat announced the upcoming availability of Red Hat Enterprise Linux 10.2 and Red Hat Enterprise Linux 9.8. The new versions build on the cap...
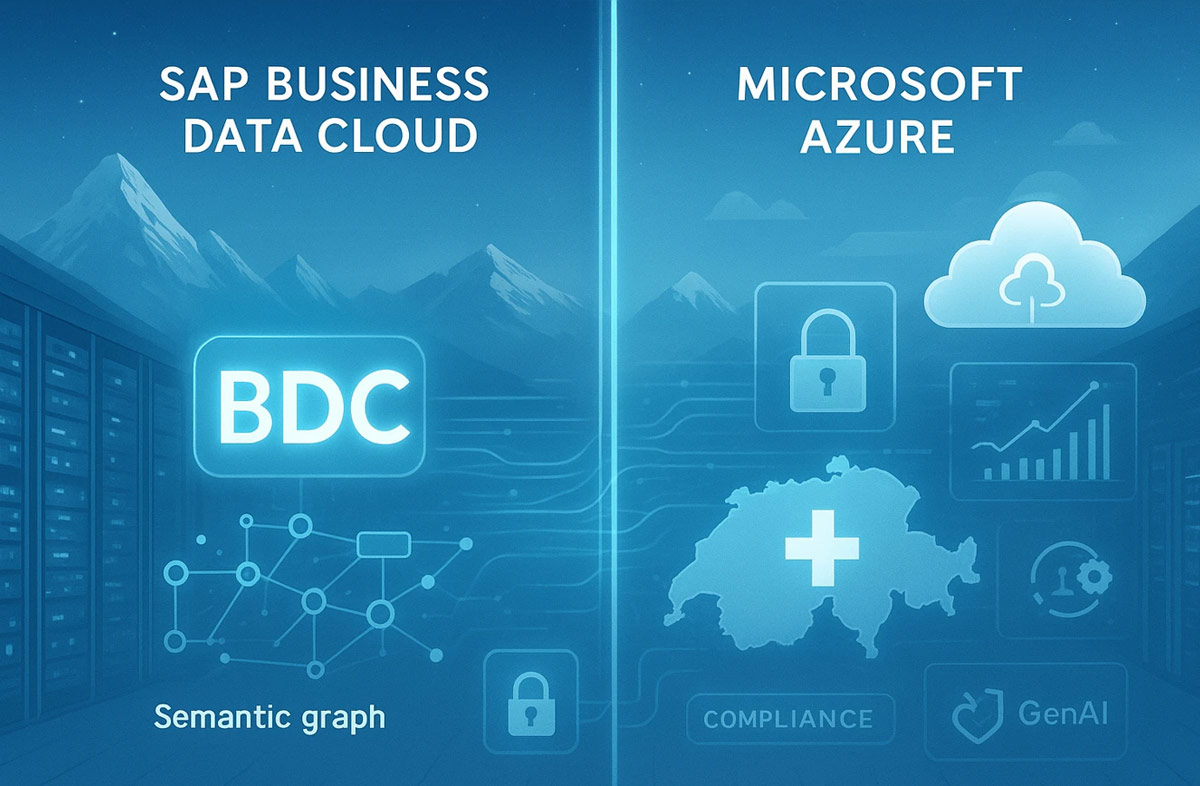
SAP and Microsoft announced that in the coming weeks SAP Business Data Cloud (BDC) will become available in Microsoft Azure data centers in Swit...
Huawei introduced new F5G-A solutions and products during the Huawei Intelligent Africa Congress 2026 in Cairo, Egypt. As part of the event, the...